Overview
This project presents a secure distributed computation architecture designed to protect sensitive data from hardware Trojans embedded within third-party manufactured chips. The system leverages Multi-Party Computation (MPC) and Shamir’s Secret Sharing (SSS) to ensure that no single compromised device can reconstruct confidential data.
The core objective was to design and implement a scalable system that:
- Operates normally under standard workloads
- Protects internal data from hardware level attacks
- Maintains acceptable performance and power overhead
- Uses affordable, practical hardware
Problem Motivation
Modern chip manufacturing often involves third-party fabrication, introducing the risk of malicious circuit modifications known as hardware Trojans. These Trojans can leak data, alter computation, or remain dormant until triggered.
Traditional detection methods:
- Do not detect all Trojan types
- Require expensive equipment
- Do not scale efficiently
Instead of relying solely on detection, this project focuses on architectural resilience, designing a system where even a compromised chip cannot access usable data.
System Architecture
High-Level Design
The architecture consists of:
- 1 Trusted Node (FPGA-based)
- 3 Agent Nodes (FPGA-based)
- Ethernet-based communication (IEEE 802.3 compliant)
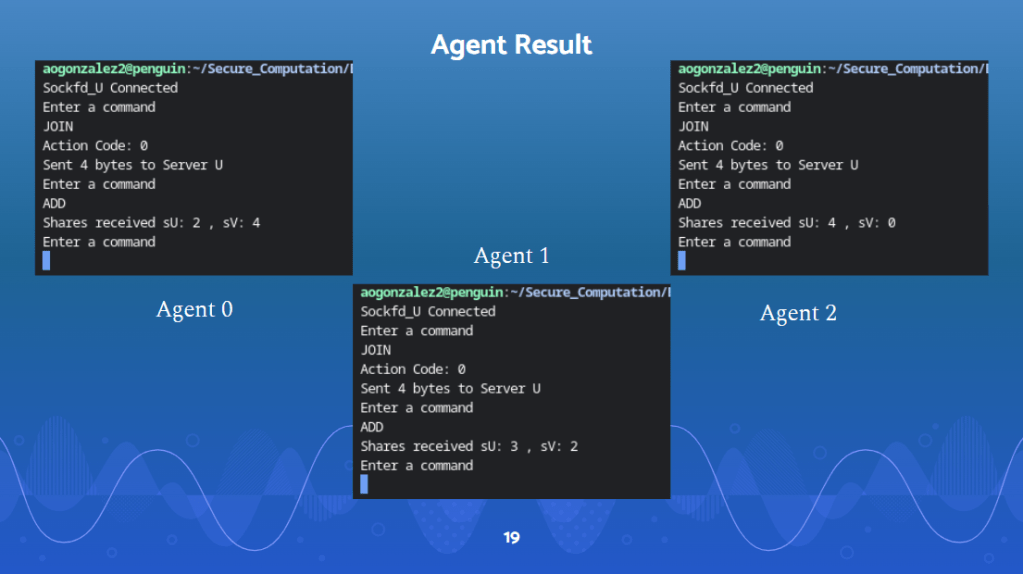
- The Trusted Node distributes encrypted shares to agents.
- Agent Nodes perform computations only on secret shares.
- Agents cannot communicate with each other.
- Only the Trusted Node reconstructs the final result.
- The Trusted Node distributes encrypted shares to agents.
- Agent Nodes perform computations only on secret shares.
- Agents cannot communicate with each other.
- Only the Trusted Node reconstructs the final result.
This strict communication topology prevents reconstruction of secrets by compromised agents.
Hardware Implementation
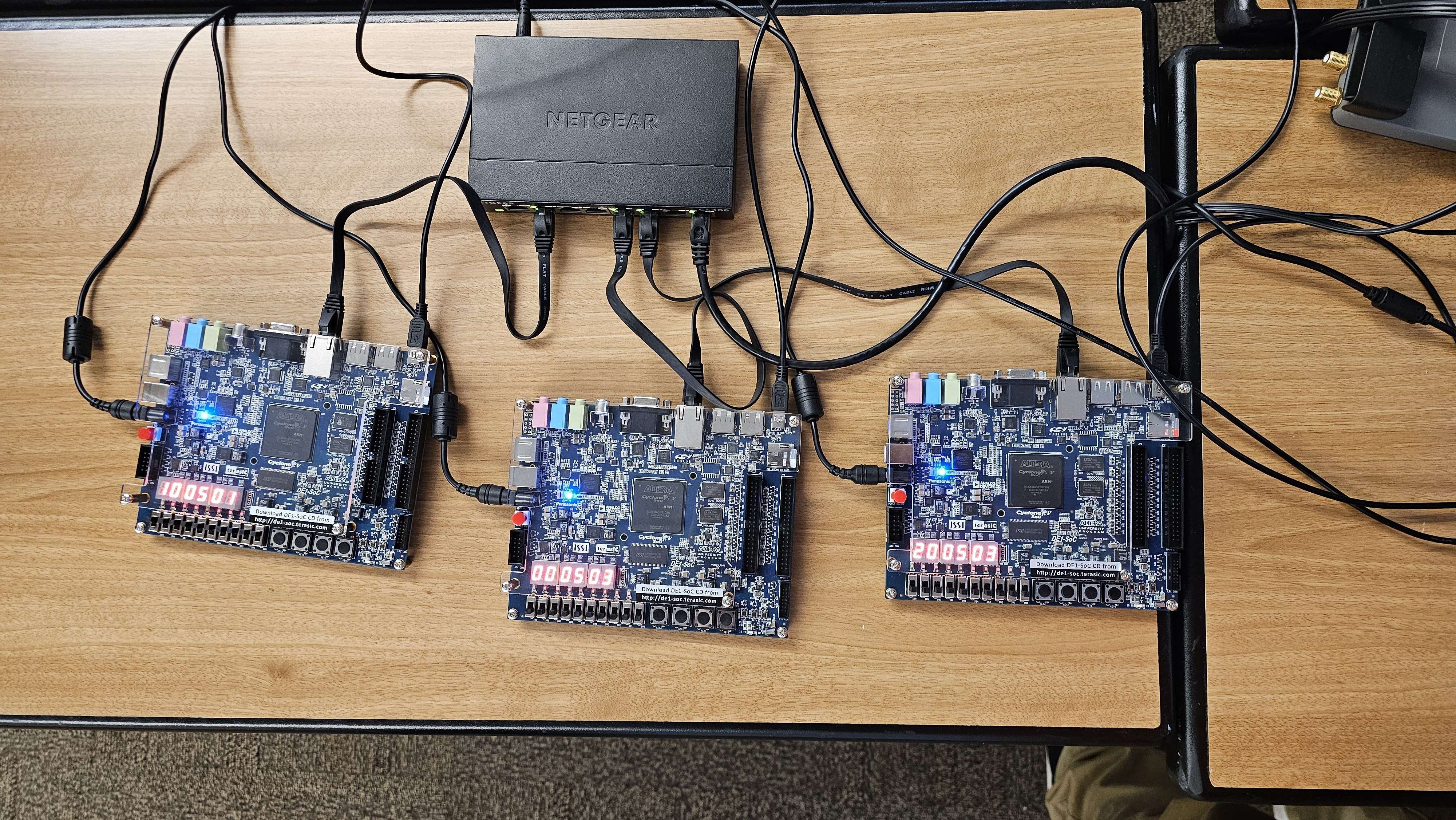
The system was implemented using:
- Altera DE1-SoC FPGA boards
- ARM Cortex-A9 processors
- HPS–FPGA bridge communication
- Ethernet networking via switch
- Linux OS on onboard processors
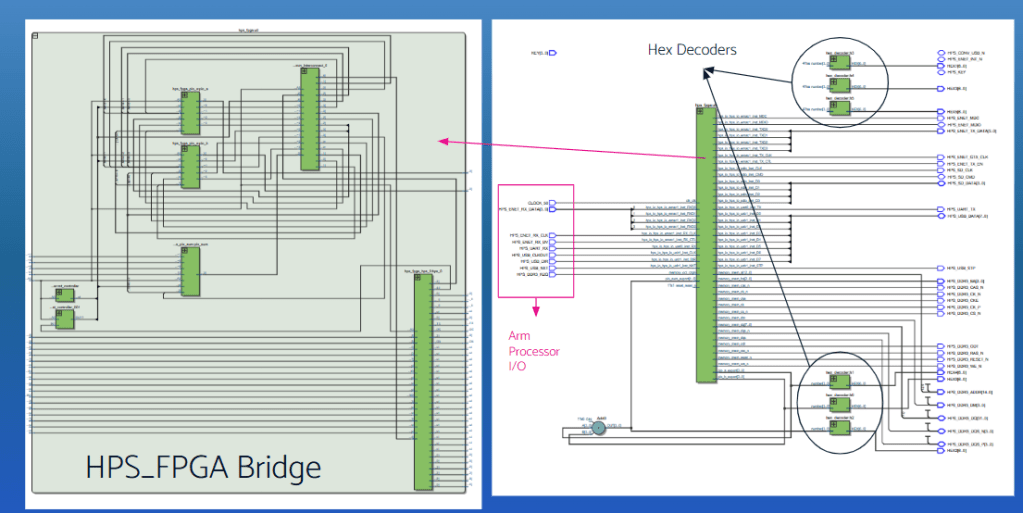
Node Responsibilities
Trusted Node:
- Receives user input
- Generates secret shares
- Distributes shares to agents
- Reconstructs final result
- Contains memory, control unit, ALU, secret generator, and solver
Agent Nodes:
- Contain specialized ALUs for SSS-domain arithmetic
- Perform secure computation
- Never hold full plaintext data
Even if an Agent Node is compromised, leaked data appears as unusable encrypted garbage.
Results & Impact
Testing demonstrated:
- Successful generation and reconstruction of encrypted shares
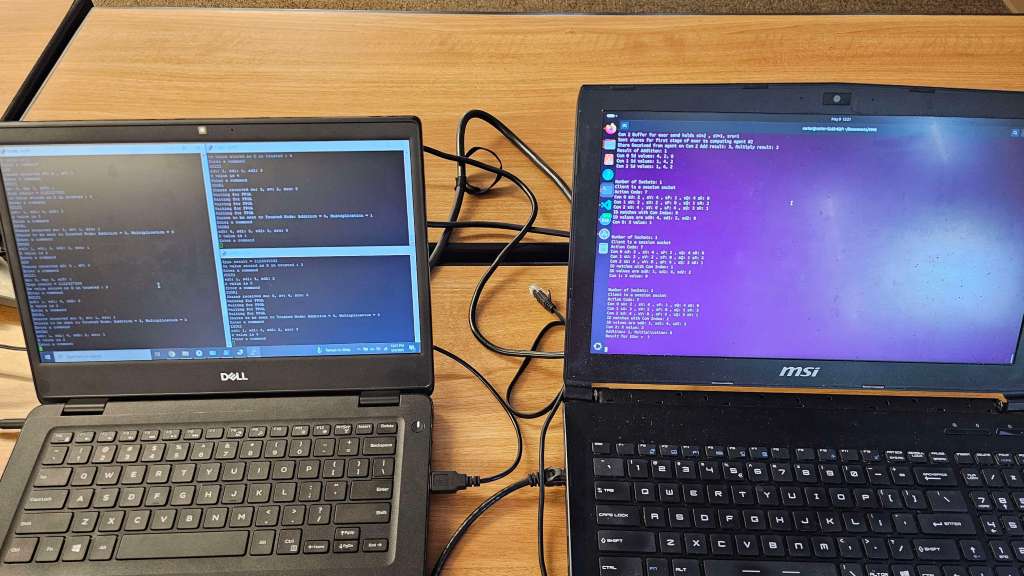
- Correct secure computation across distributed FPGA nodes
- Functional Ethernet-based communication
- Secure isolation of agent nodes